Agiboo.com Website Vulnerability Disclosure Program (VDP) Policy
Overview
Agiboo is committed to ensuring the security of our customers by protecting their information from unwarranted disclosure. This policy is intended to give security researchers clear guidelines for conducting vulnerability discovery activities and convey our preferences as to how to submit vulnerabilities discovered.
This policy describes what systems and types of research are covered, how to send vulnerability reports, and how long security researchers should wait before publicly disclosing vulnerabilities.
We want security researchers to feel comfortable reporting vulnerabilities, so they can be fixed. This policy has been developed to reflect our values and uphold our sense of responsibility to security researchers who share their expertise with us in good faith.
Authorization
If you make a good faith effort to comply with this policy during your security research, we will consider your research to be authorized, work with you to understand and resolve the issue quickly and will not recommend or pursue legal action related to your research. However, we do not offer monetary rewards for vulnerability disclosures.
Guidelines
Under this policy, “research” means activities in which you:
- Notify us as soon as possible after you discover a real or potential security issue
- Make every effort to avoid privacy violations, degradation of user experience, disruption to production systems, and destruction or manipulation of data
- Only use exploits to the extent necessary to confirm a vulnerability’s presence. Do not use an exploit to compromise or exfiltrate data, establish command line access and/or persistence, or use the exploit to “pivot” to other systems
- Provide us a reasonable amount of time to resolve the issue before you disclose it publicly
- Do not intentionally compromise the privacy or safety of Agiboo personnel, customers, or third parties
- Do not intentionally compromise the intellectual property or other commercial or financial interests of any Agiboo personnel or entities, customers, or third parties.
Once you have established that a vulnerability exists or encounter any sensitive data (including Personally Identifiable Information (PII), financial information, proprietary information, or trade secrets of any party), you must stop your test, notify us immediately, and not disclose this data to anyone else.
Scope
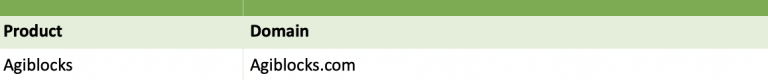
All systems and services associated with the domains listed are in scope, including any subdomains and any website with a link to this policy.
Vulnerabilities found in non-Agiboo systems are out of scope and should be reported directly to the vendor in accordance with its own Vulnerability Disclosure Program (VDP) Policy (if any).
Though we develop and maintain other internet-accessible systems or services, we ask that active research and testing only be conducted on the systems and services covered by the scope of this document. If there is a system, which is out of scope that you think merits testing, please contact us to discuss it first.
Rules of Engagement
Security researchers must not:
- Test any system other than the systems in the ‘Scope’ section (above)
- Disclose vulnerability information except as defined in the ‘Reporting a Vulnerability’ and ‘Disclosure’ sections (below)
- Engage in physical testing of facilities or resources
- Engage in social engineering
- Send unsolicited electronic mail to Agiboo personnel or customers, including “phishing” messages
- Execute or attempt to execute “Denial of Service” or “Resource Exhaustion” attacks
- Introduce malicious software
- Test in a manner which could degrade the operation of Agiboo systems or intentionally impair, disrupt, or disable Agiboo systems
- Test third-party applications, websites, or services that integrate with or link to or from Agiboo systems
- Delete, alter, share, retain, or destroy Agiboo data, or render Agiboo data inaccessible
- Use an exploit to exfiltrate data, establish command line access, establish a persistent presence on Agiboo systems, or “pivot” to other Agiboo systems.
Security researchers must:
- Cease testing and notify us immediately upon discovery of a vulnerability
- Cease testing and notify us immediately upon discovery of an exposure of non-public data
- Purge any stored Agiboo non-public data upon reporting a vulnerability.
Security researchers may:
- View or store Agiboo non-public data only to the extent necessary to document the presence of a potential vulnerability.
Reporting a Vulnerability
We accept vulnerability reports at support@agiboo.com
Information submitted under this policy will be used for defensive purposes only i.e., to mitigate or remediate vulnerabilities. If your findings include newly discovered vulnerabilities that affect all users of a product or service and not solely Agiboo, we may share your report with the Cybersecurity and Infrastructure Security Agency (CISA), where it will be handled under their coordinated vulnerability disclosure process. We will not share your name or contact information without express permission.
By submitting a vulnerability, you are indicating that you have read, understood, and agree to the guidelines described in this policy for the conduct of security research and disclosure of vulnerabilities or indicators of vulnerabilities related to Agiboo information systems, and consent to having the contents of the communication and follow-up communications stored on a Agiboo system.
To help us triage and prioritize submissions, we recommend that your reports:
- Adhere to all legal terms and conditions
- Describe the vulnerability, where it was discovered, and the potential impact of exploitation
- Offer a detailed description of the steps needed to reproduce the vulnerability (proof of concept scripts or screenshots are helpful).
Disclosure
Agiboo is committed to timely correction of vulnerabilities. However, we recognize that public disclosure of a vulnerability in the absence of a readily available corrective action increases the risk. Accordingly, we require that you refrain from sharing information about discovered vulnerabilities for 90 calendar days after you have received our acknowledgement of receipt of your report. If you believe others should be informed of the vulnerability prior to us implementing corrective action, we require you to coordinate in advance with us.
We may share vulnerability reports with the Cybersecurity and Infrastructure Security Agency (CISA), as well as any affected vendors. We will not share names or contact details of security researchers unless given explicit permission.
Verification and Remediation
The General Manager (or delegate) will be responsible for keeping an audit trail of public reports, verifications, and remediations. Verification and remediation will be assigned to the appropriate team members according to the source of the vulnerability.
Verification and Remediation Procedures
- Upon receipt of an email the Agiboo General Manager (or delegate) is responsible for calling a team meeting and deciding who should respond and the level of response.
- The level of response will include verifying the threat and communicating with the source.
- The General Manager (or delegate) will also be responsible for determining the severity of the threat e.g., the vulnerability may constitute a security incident and require involvement from other staff within the wider Volaris organisation.
Review and Revision
At a minimum, this policy will be reviewed annually or sooner if deemed appropriate. The policy review will be undertaken by Agiboo management.
